Canvas LMS Attack: The Likely Weak Point Is SaaS Authorization Boundaries
- Written: May 9, 2026 (Brisbane, Australia, AEST/UTC+10)
- Scope: Instructure Canvas LMS, not the Canva design platform
- Confidence: Medium-high. Instructure has not published a full technical root cause, so the exact exploit path should not be treated as settled.
Disclaimer: At the time of writing, Instructure has not disclosed a complete root cause. This article is not an official incident report. It is an analysis based on public reporting [1], [2], [4], [5], [7], Instructure's status page [6], university notices [8], [9], forum discussion [3], and my own security analysis experience. If Instructure later publishes more technical detail, the attribution and vulnerability classification in this article should be updated against that evidence.
Short Version
First, the naming issue: this is about Canvas, Instructure's learning management system, not Canva, the design platform. The two names are easy to mix up, and that confusion has already appeared online.
Based on the public information so far, the core story is roughly this: attackers abused an access path related to Instructure Free-For-Teacher accounts, gained Canvas data access they should not have had, and later defaced school Canvas login pages with extortion messages [1], [2], [4], [6].
I would split the incident into two layers:
- For schools, this is a third-party SaaS vendor incident and a concentration-risk problem.
- For technical root cause, it looks more like broken access control / tenant isolation failure / token-management weakness inside a multi-tenant SaaS environment.
- IDOR is possible, but not proven.
- This does not look like a traditional software supply-chain compromise. There is no public evidence of poisoned dependencies, malicious updates, CI/CD compromise, or a third-party component backdoor.
One-sentence version:
The Canvas incident appears to be an authorization-boundary failure inside Instructure's SaaS environment. The entry point was related to Free-For-Teacher accounts, the attacker gained access beyond the expected permission scope, and the later login-page defacement increased pressure for extortion.
What The Screenshots Show
Canvas Login Page Defacement
TechCrunch published a redacted screenshot showing a Canvas login page replaced with an extortion message [4].

Figure 1: Canvas login page replaced with an extortion message. Image source: [4].
UTSA Canvas Login Page
BleepingComputer's screenshot shows the utsa.instructure.com/login/canvas page displaying a ShinyHunters extortion message [2].
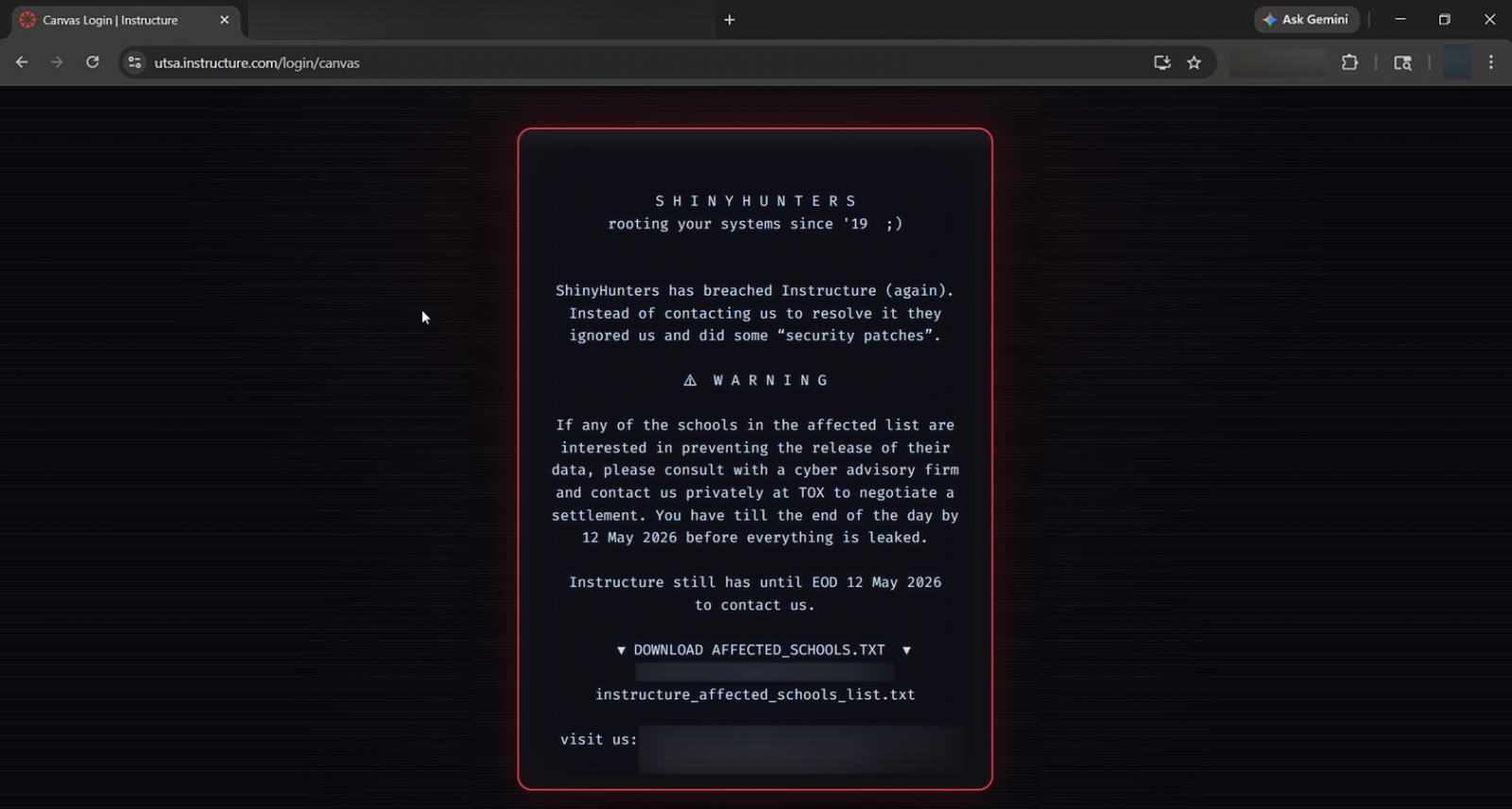
Figure 2: UTSA Canvas login page showing a ShinyHunters extortion message. Image source: [2].
School-Side Disruption Notice
AP used a Georgia Tech IT notice screenshot, showing that the incident affected normal school operations [5].
Figure 3: School-side notice about Canvas disruption and the security incident. Image source: [5].
Timeline
| Date | Event |
|---|---|
| Around 2026-04-25 | University notices suggest the attacker may have started gaining unauthorized access around this time [8], [9]. |
| 2026-04-29 | Instructure detected unauthorized activity and began revoking attacker access [6]. |
| 2026-05-01 | Instructure publicly confirmed the security incident on its status page [6]. |
| 2026-05-02 | Instructure said the incident was preliminarily contained, with privileged credentials and access tokens revoked, patches deployed, some internal keys rotated, and monitoring strengthened [6]. |
| 2026-05-06 | Instructure said Canvas was fully operational and advised customers to enable MFA, review administrator access, and rotate API tokens and keys [6]. |
| 2026-05-07 | Multiple school Canvas login pages were defaced with extortion messages. Canvas, Canvas Beta, and Canvas Test were temporarily placed into maintenance mode [2], [4]. |
| 2026-05-08 | Instructure confirmed through media that attackers abused an issue related to Free-For-Teacher accounts, and that those accounts were temporarily disabled [1], [5], [7]. |
| 2026-05-09 | A full root cause was still not public. Forum users and school-side communities were still discussing whether login should be restored and what remained uncertain [3], [6]. |
What Is Confirmed
Affected System
The affected system is Instructure's hosted Canvas LMS cloud platform. Schools, universities, and K-12 institutions are affected customers. Based on current public information, they do not appear to be the primary entry point.
Data Involved
Instructure's status page says the currently identified affected data includes [6]:
- User names
- Email addresses
- Student IDs
- Messages between Canvas users
Instructure also says it has not found evidence that the following data was involved:
- Passwords
- Dates of birth
- Government identifiers
- Financial information
Source: Instructure status page [6].
Vendor Response
Instructure has publicly stated, or confirmed through media, that it took the following actions [1], [5], [6]:
- Revoked affected privileged credentials and access tokens
- Deployed patches
- Rotated some internal keys
- Restricted token creation pathways
- Strengthened platform monitoring
- Temporarily disabled Free-For-Teacher accounts
- Took Canvas temporarily offline or into maintenance mode while investigating the login-page defacement
Those actions matter. They point away from a simple website defacement and toward credentials/tokens, authorization boundaries, account paths, and cross-tenant access controls.
How The Attack Chain Fits Together
When the public clues are put together, my current working model is:
- The attacker identified an access path related to Canvas Free-For-Teacher accounts.
- That path had a permission-boundary problem, allowing a free account to gain access beyond its normal scope.
- The attacker then accessed or invoked Canvas data export, API, or backend capabilities, pulling names, email addresses, student IDs, and internal messages [6].
- The attacker later claimed to have data from nearly 9,000 institutions [1].
- On May 7, some Canvas login pages were defaced with extortion messages [2], [4].
Step 2 is the important part. Until Instructure publishes the full root cause, it is not responsible to say whether this was IDOR, bad privilege inheritance, or a token creation path issue. But the revocation of tokens, rotation of internal keys, and restriction of token creation pathways strongly suggest that the weakness sits near the authorization boundary.
How I Would Classify The Root Cause
Safer Wording
I would not write the root cause too narrowly yet. The safer technical wording is:
The incident appears to stem from a broken access control / tenant isolation failure in Instructure's multi-tenant Canvas SaaS environment, involving the Free-For-Teacher account path and potentially token-management or API authorization weaknesses.
Why I Would Not Call It IDOR Yet
IDOR is a specific claim. To call something IDOR, we should see evidence that the attacker controlled an object identifier and used it to access an object they were not authorized to access, such as changing user_id, course_id, account_id, or report_id to retrieve another school or tenant's data.
The public information currently supports these points:
- Free-For-Teacher accounts were part of the access path.
- The attacker gained unauthorized access.
- Instructure revoked tokens and credentials.
- Data may have been taken through Canvas data export or API capabilities.
- Login pages could be defaced.
That is enough to support Broken Access Control. It is not enough to lock the classification to IDOR/CWE-639. If Instructure or a later forensic report shows object-ID enumeration or tampering across tenants, the classification can be tightened then.
Vulnerability Classification
| Classification | Fit | Notes |
|---|---|---|
| OWASP A01: Broken Access Control | High | Safest top-level category based on current evidence. |
| CWE-862: Missing Authorization | Medium-high | Fits if sensitive actions lacked authorization checks. |
| CWE-863: Incorrect Authorization | Medium-high | Fits if authorization logic existed but evaluated the wrong boundary. |
| CWE-269: Improper Privilege Management | Medium | Fits if Free-For-Teacher accounts could inherit or escalate into unexpected permissions. |
| CWE-639: Authorization Bypass Through User-Controlled Key / IDOR | Low-medium | Only fits if later evidence shows access through object ID enumeration or tampering. |
On ShinyHunters
Media and security reporting have linked the incident to ShinyHunters. The group claimed impact across nearly 9,000 schools and hundreds of millions of users, using the alleged data theft as extortion leverage [1], [2], [4].
There are a few caveats:
- Numbers such as "nearly 9,000 schools" and "231M/275M users" primarily come from attacker claims and have not been fully independently verified [1], [2].
- AP reported that Instructure/Canvas later no longer appeared on the ShinyHunters target page, but Instructure did not confirm whether any ransom was paid [5].
- BleepingComputer noted that ShinyHunters has recently targeted SaaS, Salesforce, third-party integrations, and token access paths. That does not mean this Canvas incident has been proven to be a Salesforce or third-party integration compromise [2].
The Real Risk
Not Just Downtime
The hard part is not just that "Canvas was down." If names, email addresses, student IDs, and internal messages were exported, follow-on phishing can become much more believable. Attackers can frame messages around exams, grades, assignment extensions, account recovery, or urgent IT notices.
The login-page defacement also matters. It suggests the attackers were not only trying to steal data; they were trying to create public pressure. For schools, this touches exams, assignment submission, grade release, and student-teacher communication.
Likely Follow-On Risks
- Password reset phishing that impersonates school IT or Canvas
- Malicious links sent as if they came from teachers or students
- Social engineering based on student IDs, email addresses, and course relationships
- More convincing scams built from Canvas message content
- Privacy risk where minors or sensitive communications are involved
Is This A Supply-Chain Attack?
It is tempting to label every vendor-side incident as a supply-chain attack, but the wording should be split:
| View | Assessment |
|---|---|
| School / university risk management | Yes. This is a third-party vendor incident and a broad supply-chain concentration risk. |
| Technical attack method | Not currently a confirmed traditional software supply-chain compromise. |
| SaaS security model | Better described as a multi-tenant SaaS platform control failure. |
| Customer responsibility | No public evidence currently shows that school-side misconfiguration caused the main incident. |
If this had to go into a formal report, I would write it as:
This is best described as a vendor-side SaaS security incident and supply-chain concentration risk for educational institutions, rather than a confirmed software supply-chain compromise.
What To Do Next
For schools and institutions:
The first priority is privileged accounts and integration credentials. Canvas administrator accounts should enforce MFA. Canvas API tokens, LTI keys, developer keys, and related integration credentials should be rotated where appropriate. Recent administrator activity, token creation records, and unusual API calls should be reviewed.
The second priority is communication. Schools should tell students and staff not to log in through email, SMS, or unfamiliar form links. Account recovery, exam delay notices, and grade-related communications should be verified through official school channels. Institutions handling minors or sensitive communication should run a privacy impact review.
The third priority is getting precise information from Instructure: whether the institution was affected, which fields were involved, what the exposure window was, and whether logs or IOCs are available. Without that, school-side response remains guesswork.
For individual users:
There is not much an individual user can fix at the platform layer, but a few steps are useful: access Canvas through the school website or a saved bookmark, do not click login links from email or SMS, do not approve unexpected MFA prompts, and change passwords on any other sites where the Canvas password was reused.
Final Assessment
This was not a normal outage. It combines data exposure, extortion, login-page defacement, and multi-tenant SaaS authorization risk.
My current attribution is:
Instructure Canvas suffered a vendor-side multi-tenant SaaS security incident caused by a broken access control or authorization-boundary failure associated with Free-For-Teacher accounts. The incident enabled unauthorized access to user data and was followed by login-page defacement for extortion. IDOR remains plausible but unconfirmed.
References
[1] Abrams, L. (2026a, May 5). Instructure hacker claims data theft from 8,800 schools, universities. BleepingComputer. https://www.bleepingcomputer.com/news/security/instructure-hacker-claims-data-theft-from-8-800-schools-universities/
[2] Abrams, L. (2026b, May 7). Canvas login portals hacked in mass ShinyHunters extortion campaign. BleepingComputer. https://www.bleepingcomputer.com/news/security/canvas-login-portals-hacked-in-mass-shinyhunters-extortion-campaign/
[3] Expensive-Jaguar2344. (2026, May 9). Tons of new info on the hack [Online forum post]. Reddit. https://www.reddit.com/r/canvas/comments/1t7dddq/tons_of_new_info_on_the_hack/
[4] Franceschi-Bicchierai, L., & Whittaker, Z. (2026, May 7). Hackers deface school login pages after claiming another Instructure hack. TechCrunch. https://techcrunch.com/2026/05/07/hackers-deface-school-login-pages-after-claiming-another-instructure-hack/
[5] Hollingsworth, H., & Williams, C. (2026, May 8). Canvas system is online after a cyberattack disrupted thousands of schools. AP News. https://apnews.com/article/canvas-cyberattack-outage-college-446c240d5aeb1b1a1e3795fb92237563
[6] Instructure. (2026, May 6). Confirmed security incident [Incident report]. Instructure Status. Retrieved May 9, 2026, from https://status.instructure.com/incidents/9wm4knj2r64z
[7] Ma, A., & Grantham-Philips, W. (2026, May 8). A Canvas outage tied to a cyberattack has wreaked havoc on colleges' final exam season. AP News. https://apnews.com/article/canvas-outage-college-students-exams-grades-209a51692f043a959459dbe37fb34e4b
[8] Princeton University Office of Information Technology. (2026, May 8). Instructure security incident update. Retrieved May 9, 2026, from https://oit.princeton.edu/instructure-security-incident-update
[9] Rutgers University Canvas. (2026, May 6). Update: Nationwide security breach involving Canvas. https://canvas.rutgers.edu/2026/05/06/update-nationwide-security-breach-involving-canvas/